|
In this issue FREEWARE SPOTLIGHT: Cryptomator — a little foil on your head is quite fashionable Additional articles in the PLUS issue • Get Plus! PUBLIC DEFENDER: Google explains why videos sent from iPhones look so terrible LINUX: The state of Linux in 2022 ON SECURITY: Ready to patch your car?
FREEWARE SPOTLIGHT Cryptomator — a little foil on your head is quite fashionable
By Deanna McElveen You can say you don’t trust the cloud with your files, but you do store files in the cloud. Your emails, your cat pictures on Facebook, your virtual farm in Farmville, your credit info, your bank account … yep, the cloud. But you don’t have to go all-in with full trust. Take matters into your own hands! I love my cloud storage services. I use Dropbox (my favorite), Google Drive (or whatever they’re calling it this week), OneDrive (will always be SkyDrive in my heart), and iCloud (we all make mistakes). Do I trust them to encrypt my data? Sure I do. Encrypt away, geeks! Do I also encrypt the files again from my end? Heck, yeah! Now, one might call me paranoid, but I’m really just a bit of a history buff. Words like “unhackable” and “uncrackable” sound an awful lot like “unsinkable” to me. “Deanna, why should I encrypt my files if these cloud services are already doing that?” Simple. They do encrypt your files, but they also hold the encryption keys (aka the secret decoder ring). Did they give you a key? They didn’t give me a key. Where do they store this key? In what server and in what country? If it’s all the same to you, I’ll just encrypt them first and keep my own key, thank you. Tobias Hagemann, Sebastian Stenzel, and Christian Schmickler (Figure 1) are the founders of Skymatic of Bonn, Germany. When not winning awards, they and their team develop, and give freely to the world, an open-source program called Cryptomator.
Cryptomator is crazy easy to use. In a nutshell, you are creating a folder in your cloud storage folder that Cryptomator calls “The Vault.” The AES 256-bit encryption is automatic and on the fly. Cryptomator will create a virtual drive in Windows Explorer to access your vault. You just move or copy your super-secret files and folders to it — and Cryptomator does the rest. Get Cryptomator for Windows, MacOS, or Linux from OlderGeeks.com, then fire-up the program to begin installation (see Figure 2). I could just tell you to check I agree to the license terms and conditions and start the install, trusting that I read it and will tell you it’s all good. I could, but you really must read the terms and conditions yourself before installing anything. Always.
Okay, all installed? Let’s learn how to use it in Windows (not much different in MacOS or Linux). Open Cryptomator from your Start Menu to get the first window to set things up (see Figure 3).
When the Add Vault window pops up, choose Create New Vault (see Figure 4).
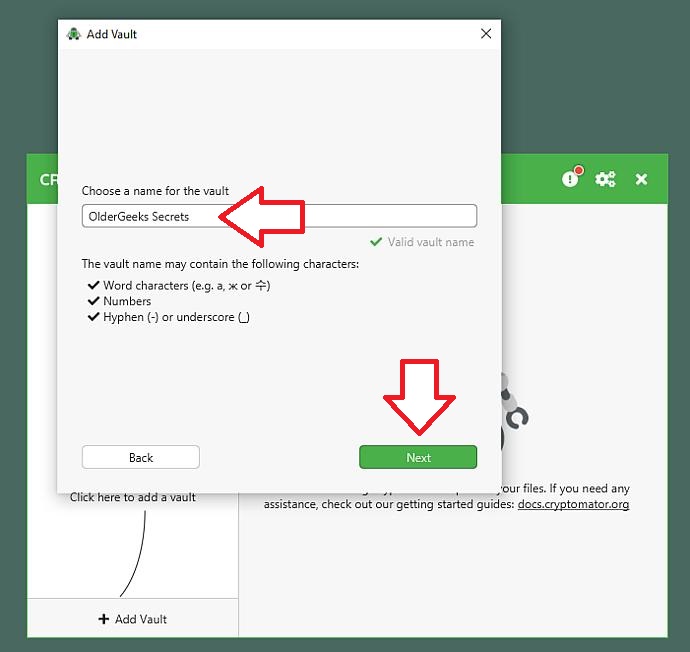
Next, give your vault a name (see Figure 5). You are allowed to include word characters, numbers, hyphens, and underscores — so go nuts. I, however, am not nuts, so mine is pretty straightforward. If the green checkmark appears next to Valid vault name, your new vault name is good.
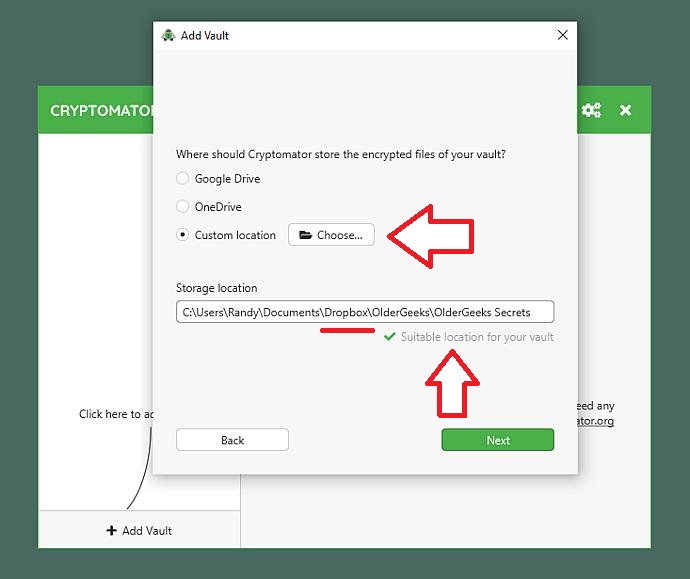
Now you will select your storage service. One note on Dropbox here: From what I can gather from testing on a newly built laptop and hubby’s computer (from which these screenshots were taken), Dropbox shows up only if it’s a relatively new install. If Dropbox has been on a computer for years, you must browse to your Dropbox folder by choosing Custom location (see Figure 6). (Some time ago, Dropbox must have made changes to the way things are stored, and Cryptomator can’t detect such older installs.) I chose to place my vault called “OlderGeeks Secrets” into an existing folder called “OlderGeeks” in Dropbox.
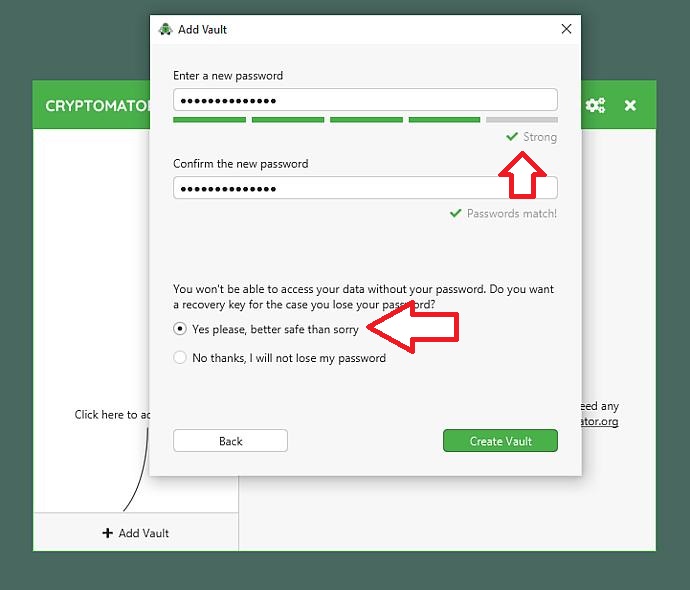
Create a strong password (see Figure 7). Cryptomator will show you, as you type it, how lame your password is. Keep typing things until Cryptomator indicates that it is not lame. I have learned that my biggest trouble with growing old is forgetting that I forget things. My brain tells me to create a super-complicated password here and not to worry about forgetting it. Luckily, I remember that I forget that I forget things. This is why I, and you, are going to check the box that Yes please, better safe than sorry when asked if we want to create a recovery key.
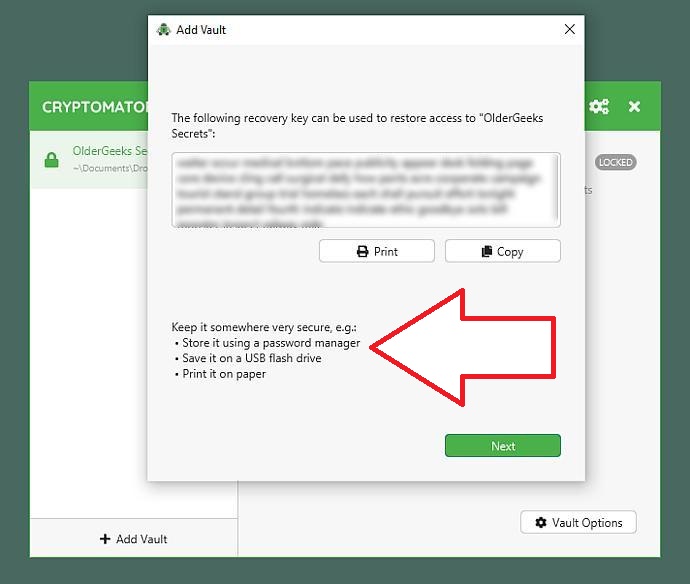
When your recovery key comes up (mine is blurred here), you can print it or copy it to the Windows Clipboard for pasting into a document. (See Figure 8.) Don’t feel insulted when I say the following: Do not paste it into a document that is stored in your cloud service folders! Use a flash drive, and keep it in a safe place.
After clicking Next, the next window (not shown here) will ask if you want to unlock your vault now or later. Go ahead and unlock it. After doing so, you will get a pop-up dialog to enter your password (see Figure 9). You can check the box to remember your password, but don’t. If someone steals your computer, they won’t even have to look for a recovery key if you made it easy for them by checking the Remember password box.
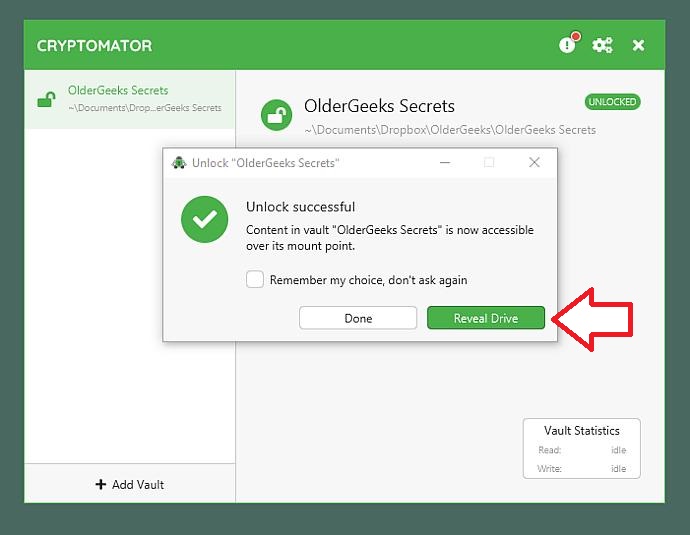
Next, you need to click Reveal Drive (see Figure 10) if you want your new virtual drive (with its new drive letter) to open right away. If you click Done instead, you will need to browse for the new drive.
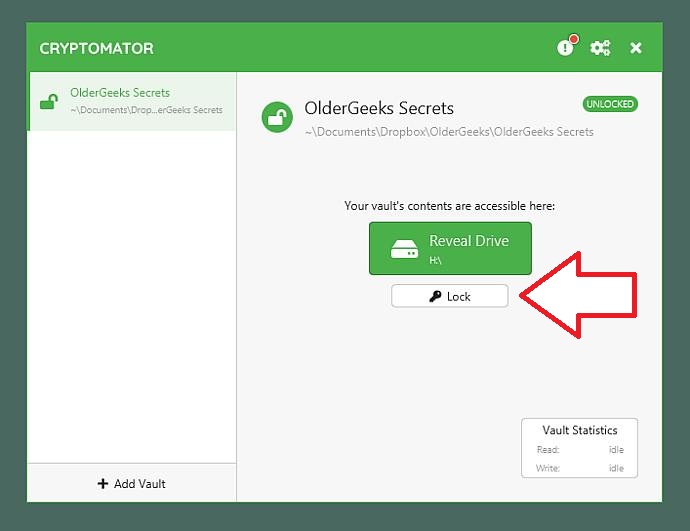
Now I have a new drive H: (see Figure 11). It’s a virtual drive that is actually the new folder I created in Dropbox. This is where I can start adding folders and files. As you can read in the “WELCOME.rtf” file, do not make any changes to your vault folder through DropBox or directly through the Dropbox folder in Windows Explorer. If you do, your files will not get encrypted, and it will probably create a big mess. Any other files or folders in any cloud storage can still be used as you always have — just not the vault folder(s).
To relock the virtual drive, just click Lock (see Figure 12). This makes the virtual drive (my H: drive) disappear from Windows Explorer. Simply use Cryptomator to browse your virtual drives that are invisible to Windows and unlock them as needed.
Now you can start adding files and folders to this drive, just like you would with any drive — but remember not to go too crazy at first. Everything you add still has to sync with the cloud. Under Settings, there are a few useful items — such as the ability to start the program with Windows, minimizing the program on start, and the choice to have Cryptomator lock all drives automatically when you close the program. This one is going onto all of our machines to stay. Hope you find it useful, too! Bonus Software!
I discovered it. I can’t stop playing it. I’m addicted to it. It’s silly. It’s a big waste of time. Now Munchy Worm is your problem, too. Get Munchy Worm from OlderGeeks.com!
Happy computing!
Deanna and Randy McElveen are celebrating more than a decade of running OlderGeeks.com, over two decades in the computer business, and even more than that putting up with each other. Their computer store is in a small town in the Missouri Ozarks. Believing that happy customers are always the best advertisement, they hope to squeeze in a couple more decades doing the same.
The AskWoody Newsletters are published by AskWoody Tech LLC, Fresno, CA USA.
Your subscription:
Microsoft and Windows are registered trademarks of Microsoft Corporation. AskWoody, AskWoody.com, Windows Secrets Newsletter, WindowsSecrets.com, WinFind, Windows Gizmos, Security Baseline, Perimeter Scan, Wacky Web Week, the Windows Secrets Logo Design (W, S or road, and Star), and the slogan Everything Microsoft Forgot to Mention all are trademarks and service marks of AskWoody Tech LLC. All other marks are the trademarks or service marks of their respective owners. Copyright ©2022 AskWoody Tech LLC. All rights reserved. |
||||||||||||||||||||||||