In this issue SAFETY: Anatomy of a malware Additional articles in the PLUS issue PUBLIC DEFENDER: Buy the drives you need before ‘chia’ gets them all LANGALIST: From bad to worse: A repair goes awry BEST UTILITIES: Freeware Spotlight — O&O Lanytix ON SECURITY: Is the cloud unsafe?
SAFETY Anatomy of a malware
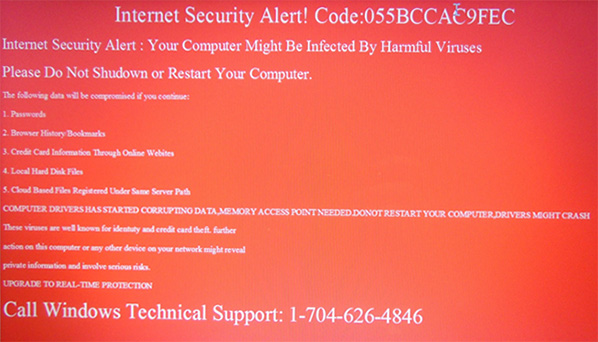
By Ben Myers Things are not always as they seem. What might appear to be a devastating, PC-destroying piece of malware can sometimes be a spoof. Recently, a client gave me his laptop, which displayed a frightening message as soon he logged in (see Figure 1). This variety of malware is all too popular. Here is a step-by-step process to remove it, expecting that the antivirus software installed in the computer cannot do its job. Along the way, you will see where malware is often hidden.
And, NO! The malware did not do as it claimed. But it hoped to scare owners into calling the area-code 704 number at the bottom of the screen, a cellular number in the Charlotte, North Carolina area. The scammer on the phone would hope to take your credit-card information and run up some charges. At the heart of this scam is software called Supremo, claimed to be remote-access software similar to RDP, AnyDesk, TeamViewer, UltraVNC, LogMeIn, and others. Like those programs, Supremo allows the scammer to gain remote access to your computer, after which your passwords and personal financial information are at serious risk of theft. Beware! You can find very positive reviews of Supremo via a Google search, as well as possibly bogus or obsolete instructions for its removal. Supremo may have an honest and legitimate purpose, but its association with this malware is an enormous red flag. The first breakthrough
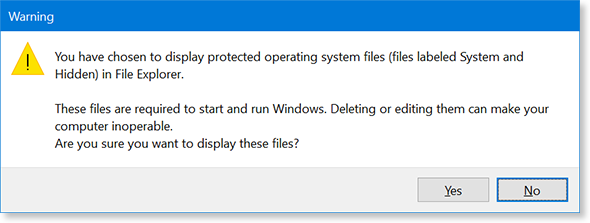
The initial screen displayed was much larger than shown, with the telephone number below the bottom of the screen. There is nothing to lose by trying the usual browser shortcut Ctrl+Minus to shrink the text size. Surprise! This worked, so the red screen appeared in a browser window. Next, Ctrl+Alt+Del was not inhibited. It brought up the usual choices, so I clicked Task Manager, after which the laptop looked and behaved normally, except for the red screen in the background. Great! I was able to click the start menu, run programs, and terminate programs unimpeded. Often there are nasty files with a hidden attribute lurking in various folders. When examining a computer for malware or a virus, unhide protected operating-system files and show hidden files, folders, and drives as follows:
Remember to hide files and folders again when this spelunking expedition is over. Clean up
Before doing anything further, take the time to clean up the system.
%temp% is the folder where many Windows programs store data temporarily and, like little children, do not clean up after themselves. If thousands of files and folders are allowed to accumulate in %temp%, a system will simply crawl. (On my workstation, %temp% expands to C:\Users\benmy\AppData\Local\Temp.) A Discovery
Continuing with the same Windows Explorer window you have been using, follow these steps:
C:\windows\temp is the other folder used for temporary files created by both Windows and some Windows apps. It gets just as little attention as %temp% and thus accumulates just as much detritus. Here’s the very interesting discovery. After deleting all possible files from Windows’ own temp folder(s), this infected system still showed the folder SupremoRemoteDesktop. That means it was in use, a vital clue about the malware. By proxy
The next step was to use the Chrome browser to find out more about this scam. Chrome complained that it could not access the Internet and suggested fixing the laptop’s proxy settings. To do this, click Settings (for Windows, not Chrome), then Network and Internet, and, finally, Proxy. The proxy settings on this laptop were definitely unusual, with Use setup script set to On and a Script address of nbgvjgjgdjfjf, which makes no sense at all. Clear the Script address field and change Use setup script to Off. The radio button Use a proxy server was set to On with an address of http://gjgjfgjgfgfjjggj using Port 80. These values are nonsense, too, so clear both the address and the port, then set Use a proxy server to Off. Once again, Windows will be unable to delete files in use by apps that are currently running, and it will present a dialog box asking what you want to do. Check Do this for all current items and then click Skip. The seemingly random proxy information serves no additional purpose beyond blocking Internet access, a move clearly designed to cause more panic on the part of the user — assuming he or she ever gets this far. After resetting the laptop’s proxy, I downloaded the latest free CCleaner program and used it to clean up files and the Windows registry. After the cleanup, it was time to see what Task Manager showed about Supremo. There were no programs running with that name, but the processes Supremo, Supremo Helper, and Supremo Service needed to be terminated. Once the Supremo processes were terminated, it was possible to go back to C:\windows\temp and delete the folder SupremoRemoteDesktop and its contents, the programs responsible for the services. Finally, I emptied the Windows recycle bin of all this junk. Why all the cleanup effort? For one thing, eliminating all these files reduces the time and effort required by your everyday virus- and malware-scanning apps. More importantly, files deleted during this process are extremely unlikely to be part of the malware. That’s because the malware’s files cannot be deleted while it is running; in effect, inability to delete is the detection method used by this approach. Making sure
To be sure Supremo and all of its parts were nailed, I first downloaded Trend Micro’s HouseCall to scan for viruses. In this case, HouseCall found nothing. To be really sure, I also downloaded the trial version of Malwarebytes. It found one harmless bit of the malware — the threatening display of the red screen — which was just an image. To be sure a computer is truly back to normal, reboot it several times and use it a bit to see whether there are still any ill effects. Finally, reverse the File Explorer options, putting them back to their customary settings. What caused Supremo to find its way into this laptop? Whatever the client did happened before he powered down and then powered up the laptop again to see the screen with the red background. Tracing the exact cause without a Windows flight data recorder is well-nigh impossible. Be careful what you click, especially in emails. Epilogue
Here is a short list of folders in Windows computers where malware and viruses are often found.
This particular malware variant buried itself inside Windows as services, so there was no need for it to add programs to the startup list or to create a folder for iteself in C:\Program Files (x86). Other kinds of malware and virus software find other places to hide themselves, often creating hidden folders. As we figure out how to remove some species of malware, the perpetrators play whack-a-mole with us and move its various files and folders around. Google searches revealed several sets of instructions for the removal of Supremo, but these were decidedly different from what I did, possibly because an earlier version than this one had installed itself differently. Sometimes the developers of antivirus and antimalware are playing catch-up with us. The best antivirus and antimalware protection is between your ears. Be careful what you click!
For over 20 years, Ben Myers has offered “cradle-to-grave” computer services for small businesses and individual computer owners — including building, upgrading, refurbishing, testing, repairing, and recycling of computer and network gear, primarily with Windows, some MacOSes, and Linux.
You’re welcome to share! Do you know someone who would benefit from the information in this newsletter? Feel free to forward it to them. And encourage them to subscribe via our online signup form — it’s completely free!
Publisher: AskWoody Tech LLC (sb@askwoody.com); editor: Will Fastie (editor@askwoody.com). Trademarks: Microsoft and Windows are registered trademarks of Microsoft Corporation. AskWoody, Windows Secrets Newsletter, WindowsSecrets.com, WinFind, Windows Gizmos, Security Baseline, Perimeter Scan, Wacky Web Week, the Windows Secrets Logo Design (W, S or road, and Star), and the slogan Everything Microsoft Forgot to Mention all are trademarks and service marks of AskWoody Tech LLC. All other marks are the trademarks or service marks of their respective owners. Your subscription:
Copyright © 2021 AskWoody Tech LLC, All rights reserved. |