|
ISSUE 17.12.0 • 2020-03-30
The AskWoody PLUS Newsletter
In this issue ON SECURITY: COVID-19: The challenges of working from home BEST OF THE LOUNGE: The telemetry of data collection LANGALIST: Win10 update breaks a USB modem? PATCH WATCH: Win10 optional updates placed on hold BEST UTILITIES: Freeware Spotlight — A Thousand Words On Security COVID-19: The challenges of working from home
By Susan Bradley “Social distancing” — such a simple-sounding phrase. But it’s having a titanic impact on our social and economic fabric. By any measure, we’re now living in uncertain times. With so many folks being furloughed or laid off, consider yourself fortunate if you can work from home. For those who can, there’s a wealth of online information on remote computing. Here are some highlights for making the experience effective and safe. And for all of you with kids staying home, I’ve included some information on home-learning resources. Businesses must rethink “doing business”
In a typical day, we have dozens or even hundreds of face-to-face interactions with others: at work, at stores, at bars and restaurants, at sports events, and with family and friends. But as you know perhaps too well, we’ve been asked to put all that aside in order to slow down COVID-19 infections. We’re to stay home whenever possible — and to practice social distancing when it’s not. (Yes, eventually we’ll all have to forage for “necessities.” A Whole Foods post provides examples of how stores are responding to the pandemic.) Obviously, businesses are scrambling to roll with the changes. My email inbox has been nearly overwhelmed with alerts from other organizations describing the steps they’re taking to protect employees and customers. Don’t get me wrong: COVID-19 is a serious health emergency. But it could be a lot worse. In my opinion, all businesses should use this event as a teaching moment — a test of their readiness for future emergencies. COVID-19 presents businesses large and small with a wholly new challenge: quickly setting up secure systems that will allow a record number of home-bound employees to connect to company servers. Does the company you own or work for have the technology and ability to adapt? Here are some of the steps we’re taking at my office to minimize the human interaction — both with colleagues and clients. We started by finding ways to communicate without meeting in public — for example, using conference calls instead of gathering together in a conference room. We use InterCall, but there are numerous firms that provide conference- and bridge-calling services. (Conference calls typically require one person to dial others to add them to the meeting. Bridge systems use a single phone-number/PIN combination to allow participants to call in.) Want to have a virtual face-to-face meeting? There are various tools and services that enable both sound and video. It might be as simple as FaceTime on iPhones or as powerful as corporate conferencing systems. I know of a recent family gathering held via Zoom.com. Microsoft is offering six months of Teams for free. Other examples include long-time players such as LogMeIn’s GoToMeeting, Cisco Webex, and, of course, Skype. These days, conference calling has moved well beyond business applications. I’ve heard reports that some folks impacted by the San Francisco Bay Area shelter-in-place requirements are turning to Zoom-based virtual “dates.” That might seem a bit excessive, but you’d expect the home of Silicon Valley to find a technology-based solution to “hooking up.” There’s nothing like a pandemic to establish whether that potential love interest is truly worthy of your time. Remote computing: You need the Internet but not necessarily the cloud
When it comes to actually getting work done from home, there are remote-access products and services for businesses of any size — even small firms that keep everything on the premise. Tools such as GoToMyPC, LogMeIn, and TeamViewer let you connect to your office workstation from a home computer — no cloud needed. (They are especially useful if your office PC runs on Windows and your home system is an Apple product.) The one caveat: the office workstations must be left running and connected to the Internet. These remote connections are generally secure because they primarily transmit just screen data and keyboard/mouse activity. So the risk of an infection spreading from home to office is quite low. There can be a threat from malicious keylogger programs and unsecure passwords on the home machine, but a good anti-malware app and two-factor authentication should eliminate that menace. That said, using cloud services can make working from home faster and easier. If your company has moved all applications and files online, your workflow is effectively the same no matter where you’re currently located. Between those options are the remote-access tools included with platforms such as Microsoft’s Windows Small Business Server 2008/2011 or Windows Server Essentials. Smaller businesses who are still running these systems can use Remote Web Access to connect remote machines to office workstations — again, as long as the workstations are online. (Mac users can download the latest version of Remote Desktop. An MS Docs post describes how to set it up.) There’s also a way to bypass Remote Web Access (a form of virtual private network) and connect directly to an office workstation via an RDS Server and the Remote Desktop Connection (RDC) application on a home-based system. The process assumes you have RDS Server set up at the office and have configured RDC on the home-based system (PC or Mac). Then, by merely entering the name of the target workstation, at-home workers can create a remote connection to their office workstations over SSL port 443. Note that you’re not compromising security with an open RDP port 3389 outside your network firewall. For details on this “bypass” technique, check out my AskWoody post. If you have an IT pro or consultant, you’ll want to check with them as well for other possible remote-access options. The SANS organization has several posts discussing remote computing. One titled So you’re having to work from home … caught my eye today because it suggested, among other things, using an Ethernet connection at home and not relying on local Wi-Fi. For businesses who have deployed Office 365, a Microsoft post provides detailed information on ways to manage remote-access traffic coming from work-from-home staff. For example, it might not be necessary to route all connections though the company VPN. You should also read the SANS guide on online security. Enterprise solutions: There are even more-advanced options for large businesses. See for example:
Managing documents online
If you need your clients or customers to sign official documents, tools such as DocuSign enable fully legal electronic signatures (esignatures). In fact, some of the business software I use has DocuSign built in, making esignatures an integral part of the overall document-management process. Moreover, you can photograph documents with a phone and upload the images to secure portals such as ShareFile.com, where the files can be safely shared with others. Home learning on the Net
School closures have been nearly as disruptive to our social web as business interruptions. Just like companies, teachers and parents are turning to the Internet to provide at least a minimum level of educational stability. Schools are scrambling to put classes online, and many parents are trying to balance working from home with home-learning for their kids. Helping with that task are resources such as the Khan Academy and duolingo.com. Teachers are also getting creative: my editor’s daughter is posting her own YouTube videos for her students. Just a small sampling of instructional online resources includes: And don’t forget simple ideas such as those listed in the MCLA “Remote Learning Resources for Grades PK-2” (PDF), “Remote Learning Resources for Upper Elementary PDF, and, of course … carbon-based books! With the threats to our health and finances, this is truly a scary time for most of us. But I’m reminded of the trials and tribulations my parents and ancestors lived through and survived. I have, for example, family ties that go back to the 1918 influenza pandemic — my great-uncle was just 19 when he succumbed to the flu. Grandmother often talked about her lost brother and how his death impacted her. Many families have similar stories. I only hope we can rise to the level of inspiration shown by our forebears. And I hope you and your families come though this event unscathed. Stay safe and secure!
In real life, Susan Bradley is a Microsoft Security MVP and IT wrangler at a California accounting firm, where she manages a fleet of servers, virtual machines, workstations, iPhones, and other digital devices. She also does forensic investigations of computer systems for the firm. Best of the Lounge The telemetry of data collection
Most Windows users are aware that the OS gathers activity data and then transmits that information back to Microsoft. The company states the collected telemetry is used only to improve Windows. Reportedly, the data help Microsoft understand how different PC configurations might react to OS changes. And that knowledge might point out needed Windows fixes — and also enhance future versions. The debate over Microsoft’s use of telemetry isn’t new; many Windows users have panned the policy since its inception. If the information is applied as advertised, there should be no cause for concern. But suppose you’re not comfortable allowing “unknown” data to fly off your computer … to who knows where and read by who knows whom? With that in mind, Plus member Michael Austin asks whether fellow AskWoody members know of applications, techniques, and/or services for blocking Windows telemetry — beyond the current Windows data-collection settings. Join the forum discussion. COMMUNITY The current pandemic is obviously on the minds of all AskWoody members. If you’re looking for information, related news, general discussions — or you just need somewhere to vent (politely, of course), check out the COVID-19 section. ACCESSIBILITY Plus member Wheeler started a thread seeking technology help for people with disabilities. When no responses were forthcoming, Wheeler took a different tack — and caught some needed attention. Others submitted experiences, tips, and resources. Do you have something to contribute to this important topic? Join the discussion — your suggestions might make life a bit easier for other AskWoody members. MS Office One of the most common refrains we hear from users who have upgraded to Win10 is “It worked in Win7!” Case in point: Plus member Foothills Dave purchased a new Win10 PC with Office 2019 installed. But Dave ran into an unpleasant surprise: Excel charts would not print correctly. That was never a problem on an old Win7 system. After one suggestion proved unhelpful, Dave’s ingenuity stepped in — and with some trial and error, Dave discovered a workable workaround. Security Plus member Alex5723 shares a link to a lengthy Microsoft Security blog. One of the included items announces that Windows Defender ATP is coming to Linux — and possibly to Android and Apple iOS. This is obviously an enterprise play, but forum members are still skeptical that Microsoft’s motives are altruistic. Windows 10 New to Windows 10, Plus member Tex265 is looking for ways to keep File Explorer from showing certain files, folders, and partitions in a search — as can be done in Windows 7. Some solutions are offered, but Tex265 is still looking for a simple option akin to what Win7 offers. Backup Plus member bmeacham would like to have a comprehensive and automated system backup. Specifically, bmeacham wants Macrium Reflect to automatically run immediately after Win10’s Backup and Restore (Windows 7) completes its work. Fellow Loungers offer suggestions, but the problem is still unsolved. Do you have the answer? MOBILITY The forum can host some unusual questions. For example, Plus member 280park wonders whether leaving your laptop lid open is better than closing it after each use. Are cracked hinges a good reason to leave the lid up? Fellow members are more than happy to share their experiences and practices. If you’re not already a Lounge member, use the quick registration form to sign up for free. LANGALIST Win10 update breaks a USB modem?
By Fred Langa Networking issues can be daunting, but with a little prep work and Win10’s built-in, one-click Network reset option, you can usually get things going again. Here’s what to do, step by step, to help ensure a successful repair of this and many similar networking problems. Plus: MS Office won’t let a user type the word “you”! Windows 10 no longer speaks to call-screening setup
AskWoody reader Richard Vedder suspects a recent Win10 update may have killed his spam-busting system.
From the activity I’ve seen on message boards and in support forums, Win10/USB-modem problems seem to afflict mostly older gear that’s been upgraded through one or more generations of Windows. Even if the gear and its associated software are nominally Win10-capable, various settings and software that were carried over from previous iterations can muck things up. It’s usually easy to fix using Win10’s relatively new and built-in Network reset option. The tool is easy to use and doesn’t affect anything except Win10’s networking functions. No user files or apps are touched, and the rest of your Windows setup is left unchanged. It’s not — repeat not — a full system reinstall or anything draconian like that. Highly targeted and automated, Network reset disables the currently malfunctioning networking setup and then rebuilds all existing networking connections from scratch. By starting fresh from the ground up, Network reset wipes out any problems that were carried over from previous configurations or versions. (Amusing aside: Win10’s Network reset tool actually started life in a Windows Secrets article! This new version is the successor to a click-to-run fixit that automated manual network-repair steps published in the old Microsoft document “Windows 7 Network connections are stuck in Public mode” (KB 2578723). And that article was derived from my story in the 2011-05-12 Windows Secrets column “Win7 network stuck in ‘Public’ mode.” Yes! Microsoft cribbed my step-by-step fix and the article title, too! Hah! Anyway, it’s nice to have a full network-reset tool finally baked into the operating system — even if it took almost a decade to get there!) The actual network reset begins with Step 8, below. If you’re ready to go — i.e., you have a recent backup, and you’re sure your hardware and software are current and fully Win10-compatible — you can skip ahead if you wish. But for the very best odds of success, take these preliminary steps first.
With a refreshed networking stack and current, matched, Win10-compatible drivers from top to bottom, your USB modem — along with all other Windows networking configurations — should now be functioning smoothly. MS Office is allergic to the word you!
Kenb740 reports a mysterious Office phenomenon:
That sounds like you have a bogus (or accidentally created) AutoCorrect entry working behind the scenes. All MS Office apps share the same AutoCorrect engine, so a slip of the finger that created a bad entry in any one Office app will affect all others. Here’s how to remove any entry from the Office AutoCorrect master list:
Once you’ve finished “cleaning” Office’s master AutoCorrect list, all Office apps should once again allow you to type “you” without further interference!
Fred Langa has been writing about tech — and, specifically, about personal computing — for as long as there have been PCs. And he is one of the founding members of the original Windows Secrets newsletter. Check out Langa.com for all of Fred’s current projects. PATCH WATCH Win10 optional updates placed on hold
As the world hunkers down in response to the COVID crisis, so does Microsoft. On March 24, the company announced it would pause optional non-security patches (C/D-week updates), starting in May. I assume the April releases are already mostly baked. The primary purpose of C/D-week updates — aka “previews” — is to let enterprises test non-security fixes before the formal releases go out — typically, two or three weeks later. Microsoft will reportedly continue to ship the official monthly cumulative updates, but with this announcement, the company is clearly putting its focus on critical security patching. In effect, Microsoft is acknowledging that both it and its customers already have a lot on their plates. So what exactly does that mean for small businesses and consumers? Not much, in my opinion. I invariably recommend skipping previews — and deferring Patch Tuesday releases until we get a chance to take a good look at them. (Keep this in mind: Flaws in preview patches may still turn up in the “real” cumulative updates.) Windows 7 threats: Those still running Win7 need to be aware of a new and active font exploit. So far, the attacks appear to be highly targeted and small in number. (The vulnerability is also in Win8.1 and Win10. However, there are currently no known attacks on Win8.1 systems, and Win10 has internal protections that essentially block this form of exploit.) As we noted in a March 23 AskWoody post, a bug in Adobe Type Manager Library allows remote-code-execution attacks via malicious font files. Reportedly, Microsoft doesn’t expect to fix this issue until April, at the earliest — and then only for those who have purchased ESU keys. If you are still using Win7 for general Web surfing, I recommend reading a Microsoft Advisory, which includes the following workaround:
Alternatively, if you are a subscriber to 0patch, the service has posted a micropatch for the font issue (more info). A reminder: If you don’t have current Extended Security Updates installed for Windows 7, here’s what you could be facing. Of greatest concern are the “information-disclosure” exploits that can target random Web surfing. As noted in the previous Patch Watch, none of the following vulnerabilities has been used in active attacks — yet. The bad news? Malicious hackers are using targeted zero-day exploits instead! Elevation of privilege: These Windows vulnerabilities allow malicious hackers to acquire admin rights on targeted machines. Typically, the attacker must sign in to a system, install a bogus application, and then trick a user into running the app. In most cases, the highest risk is to large businesses.
Information disclosure: These vulnerabilities allow attackers to acquire information stored in a computer’s memory. That stolen information can then be combined with other exploits. Usually, malicious hackers gain access by tricking users into opening a bogus file or webpage. Anyone who surfs the web indiscriminately is at greatest risk. It’s better to use a Chromebook or smartphone for general browsing. With the two exceptions noted below, all these vulnerabilities are in the Windows Graphics Device Interface (GDI) component.
Remote code execution: CVE-2020-0881 and CVE-2020-0883 are additional vulnerabilities in the Windows GDI. In both cases, the attacker must trick a legitimate user into opening a malicious file or website.
Tampering
If you must use Win7 — especially for business — you really want to subscribe to Microsoft’s ESU program (more info). I say that as someone who just brought back into service a retired Win7 laptop so that a co-worker could connect into the office network from home. But the best practice would be to move off Win7 and onto a newer OS. March patching summary
Reminder 1: Win10 cumulative update KB 4551762 replaced KB 4540673. Reminder 2: On Win7 systems receiving ESUs, you must have installed February’s servicing-stack update, KB 4537829, in order to add March patches. (Win7 ESUs are still available via Amy’s Harbor Computer Services sign-up form.) Reminder 3: If you don’t have February’s Windows 7 ESUs installed, Win7 and Server 2008 R2 systems are vulnerable to in-the-wild SQL Server and on-premise Exchange attacks (more info). There are other active threats, but publicly posted exploit databases still list only two:
Reminder 4: COVID-19 scams and phishing are a growing and significant security threat. There are lots of comments on the COVID pandemic in an AskWoody forum special section.
If you’re not a regular user of VPN/remote access, I recommend installing the regular March patches at this time. But skip the preview “C/D” updates released March 17 and 24. See our online Master Patch List for chronological update summaries in Excel and PDF formats. Windows 10
Servicing-stack updates Cumulative updates
.NET Framework Microsoft has been trickling out .NET updates. None has security fixes, and thus you won’t see them installed on your computer unless an app manually triggers these updates. Take a pass on the following for now.
Windows 8.1/Server 2012 R2
Windows 7/Server 2008 R2 SP1
Extended Security Updates (ESU) reminder: Be sure to install KB 4538483 from the Microsoft Update Catalog download site before attempting to add new security fixes. If you do not have this February servicing-stack update, you won’t see March’s updates. Also be sure to install the March servicing-stack update, KB 4550735, to prepare your machine for April’s fixes. Server 2012
Windows Server 2008 SP2
Office security and non-security updates
March’s Office security updates fix a remote-code-execution vulnerability. Install these patches soon. Office 2016
Office 2013 SP1
Office 2010 SP2 The following Office non-security enhancements and fixes can be installed when you’re ready. Office 2016
Office 2013 and 2010 There’s one update for Skype.
The Patch Watch updating guide
It’s a new month of patching. Once again, here are our current recommendations for patching Windows and Office. They may change as Microsoft evolves its updating process.
These days, more than ever, stay safe out there.
In real life, Susan Bradley is a Microsoft Security MVP and IT wrangler at a California accounting firm, where she manages a fleet of servers, virtual machines, workstations, iPhones, and other digital devices. She also does forensic investigations of computer systems for the firm. Best Utilities Freeware Spotlight — A Thousand Words
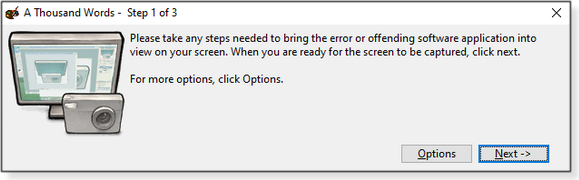
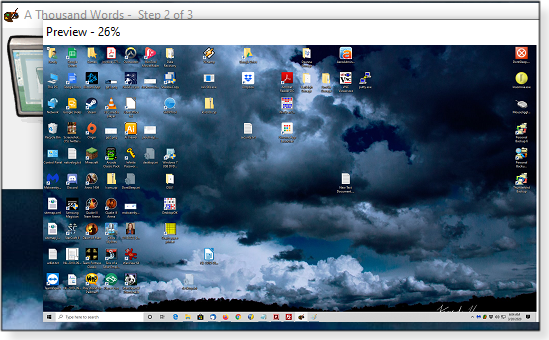
As we’re all dragged into this new pandemic reality, PC-service clients are going to need remote assistance more than ever. Unfortunately, many of those folks are not as computer-savvy as we might wish. So when users run into problems, they might find it difficult to convey what exactly is going awry. In many cases, simple screen shots will illustrate the problem far better than will describing it over the phone. Sure, a remote-control session is the most efficient means for diagnosing and possibly repairing a malfunctioning machine that’s not in front of you. But there are times when that option won’t work or is not allowed. And then there are occasions when a tech just needs some preliminary information before scheduling a remote session. The aptly named A Thousand Words (ATW) is a handy screen-capture app from developer Andrew Lambert. The tool is specifically designed to be easy to use — suitable for PC users of any skill. If a problem can be seen on-screen, the machine’s user can launch ATW and follow a simple wizard to quickly grab shots of the fault. The user can then annotate the images and email the shots to a service tech (or the unofficial family IT person). The portable program is delivered in a ZIP file that contains just the executable and a README doc. A support company can post the EXE file to its website or cloud space, and the client can simply click a link to run the tool. ATW might also be handy when you’re using a Windows-based, self-booting rescue disk and need screen captures. To start, download the ATW ZIP file from its OlderGeeks page. Once launched, the app runs the user through a short and exceptionally simple three-step process. Figure 1 shows the opening screen; Figure 2 tells the user what to do next.
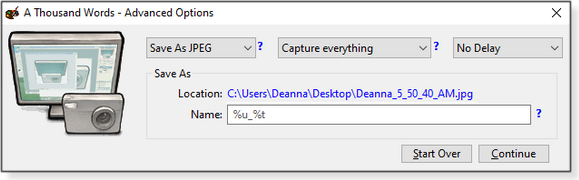
Clicking the Options button allows the user to configure ATW to various formats and tasks (see Figure 3). By default, the program saves the image to the PC’s desktop and includes a timestamp. But it’s easy to change a screenshot’s name and saved location.
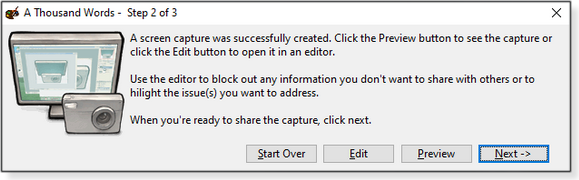
JPEG is the default image format, but you can select BMP or PNG instead. As with most screen-capture utilities, you can also choose to capture everything (the default), a specific window, or a specific screen (on multiple-screen systems). Or you can manually select a specific area. The delay option is limited to none, five seconds, or 10 seconds. In Step 2 (Figure 4), ATW lets you know the shot was made; you can now preview it (Figure 5), edit it, or try again.
ATW includes a few annotation tools. You can, for example, block out sensitive information with the Filled Rectangle tool, as shown in Figure 6. (You can change the fill color in the toolbar by clicking Tools/Change Drawing Color.) Other tools let you circle items, draw straight or freehand lines, or pick pen/fill colors with an eyedropper.
Clicking the Finish button in the third (and final) step saves any changes made to the screenshot. And in case you forgot, it shows the file’s path and name (Figure 7).
Now the client can send you the images via email, a cloud-storage link, or text message. Remote PC servicing is often a challenge. I hope A Thousand Words makes the job a little easier. Stay safe!
Deanna and Randy McElveen are celebrating over 20 years in the computer business, ten years running OlderGeeks.com, and more than 26 years of putting up with each other. Their computer store is in a small town in the Missouri Ozarks. Believing that happy customers are always the best advertisement, they hope to do it for another 20 years. Publisher: AskWoody LLC (woody@askwoody.com); editor: Tracey Capen (editor@askwoody.com). Trademarks: Microsoft and Windows are registered trademarks of Microsoft Corporation. AskWoody, Windows Secrets Newsletter, WindowsSecrets.com, WinFind, Windows Gizmos, Security Baseline, Perimeter Scan, Wacky Web Week, the Windows Secrets Logo Design (W, S or road, and Star), and the slogan Everything Microsoft Forgot to Mention all are trademarks and service marks of AskWoody LLC. All other marks are the trademarks or service marks of their respective owners. Your email subscription:
Copyright © 2020 AskWoody LLC, All rights reserved. |




 What to do: With all the rest we have on our plates, it’s good that March’s updates are relatively problem-free. I’ve not run across any issues — not even the Win10 cumulative-patch “proxy” bug. The flaw primarily impacts some enterprise deployments using virtual private networking (VPN) and Remote Desktop — see Woody’s
What to do: With all the rest we have on our plates, it’s good that March’s updates are relatively problem-free. I’ve not run across any issues — not even the Win10 cumulative-patch “proxy” bug. The flaw primarily impacts some enterprise deployments using virtual private networking (VPN) and Remote Desktop — see Woody’s  By Deanna McElveen
By Deanna McElveen